Secure Verified Hosting
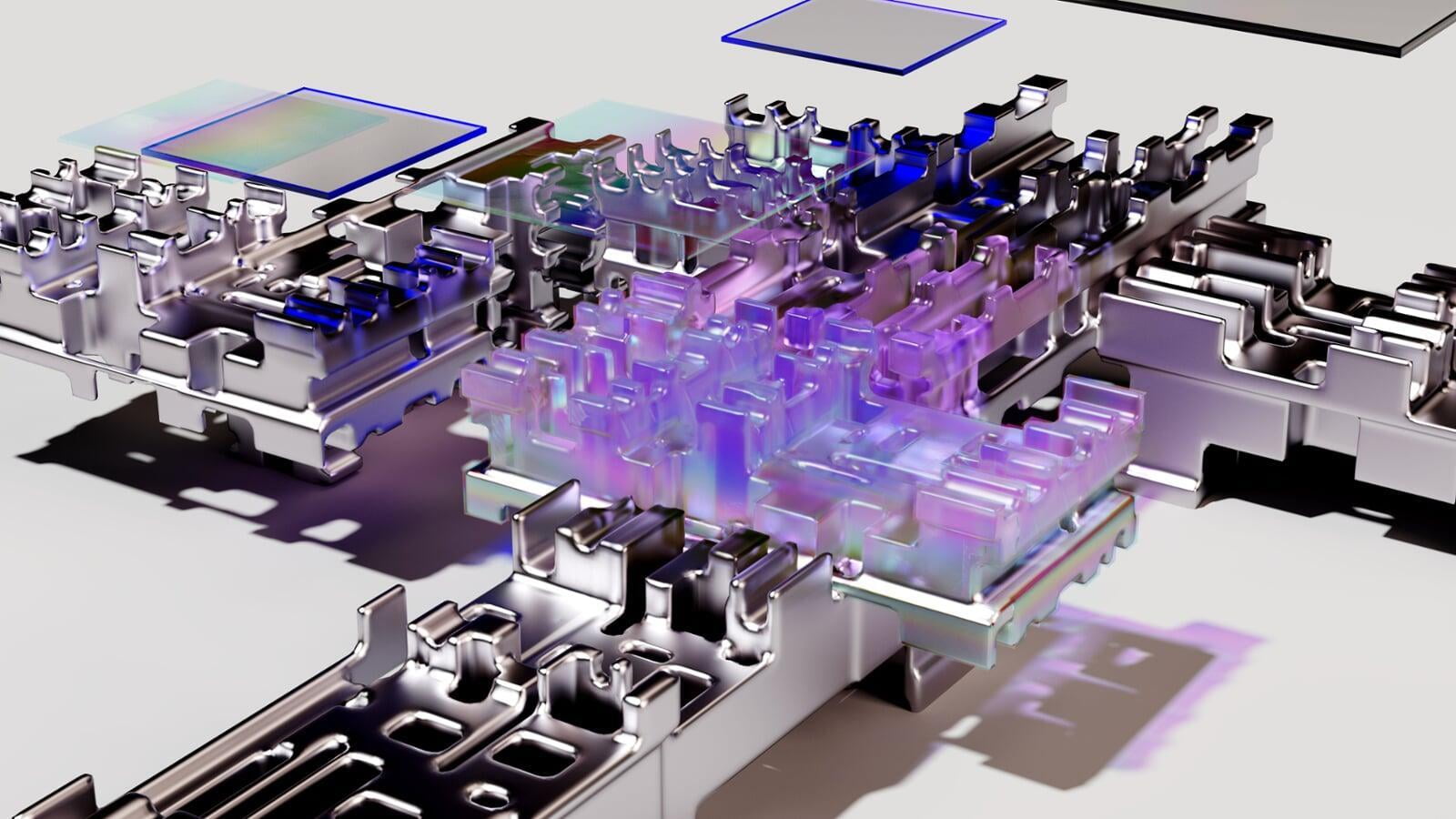
Our new Secure Verified Storage system is at the leading edge of Information Technology Security.
Research Casting International (RCI) has proven itself as the trusted custodian of many original dinosaur specimens on behalf of their museum clients, as well as the secure keeper of the physical molds used to make authorized copies and reproductions of these artifact under the strict licenses and controls agreed with museums and owners of these physical artifacts. Moving forward into the digital world, and in keeping with its skills, expertise, and experience, a new division, RCI Digital, has been created with the specific goal of maintaining RCI's role as the caretaker of significant digital data through the creation, storing, and protecting of digital artifacts securely. And though our initial emphasis is on specimens in the area of vertebrate paleontology, we intend to expand into all aspects of collections management having to do with museums and academic institutions.

RCI Digital has developed a unique and novel approach to provenance tracking of 3D scan files. Attribution is increasingly becoming one of the greatest challenges in this field. To this end, we present a permissioned private ledger-database hybrid system for registering the 'one true file' for each specimen scan on an immutable and tamper-resistant ledger and outline the life cycle of such a file throughout our system. This system also allows for credentialed queries to determine whether a file is authentic, and to allow museum institutions to mint and sell limited edition NFTs linked to the 3D scans.
Research Casting hosts a non-networked and state-of-the-art security infrastructure where all 3D data having to do with clients' assets will be stored. This is an offline database and only those with the proper security clearance can access it with any access being logged and tracked. The strongest industry protocols for cybersecurity (both physical and technological) are also in place for all things to do with these assets and all of the appropriate measures for backing the data up securely have been implemented. We will also have a SOC 2 report specific to the protection of these files that has isolated ISO 27001 standards to ensure every measure is enacted to keep the data safe and secure.